In my previous post, I discussed the decline of internet freedoms around the world. While writing the post, I realized that I should follow-up on the topic and discuss how we can use cryptography to protect our communication from surveillance by governments and corporations.
This is the first of four posts in which I discuss cryptography. If you read all four posts, you will understand the differences between symmetric and asymmetric cryptography, why the US government were against the spread of modern cryptography, how it has resulted in the first crypto war between code rebels (techno-libertarians) and the US government, and how you can easily protect your privacy using Pretty Good Privacy (PGP).
The topics of the four posts are:
- What is symmetric cryptography;
- What is asymmetric (public key) cryptography;
- The first crypto war between code rebels and the government;
- How to easily use PGP to protect your e-mail communication.
What is symmetric cryptography
The use of cryptography is more than 4,000 years old. A classic example of symmetric cryptography is the Caesar cipher. It was used by Julius Caesar for his private correspondence with his generals.
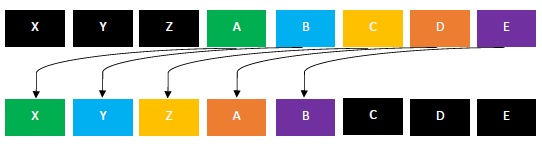
The principle of the Caesar cipher is simple. The receiver of the message has to replace each letter with another letter, some number of fixed positions down the alphabet. If a Caesar cipher, for example, makes use of a rotation of three to the left,
- A in the encrypted text becomes X
- C becomes Z
- E becomes B
- etc…
A Caesar cipher, compared to modern encryption methods, can be easily deciphered. You can for example make a frequency analysis of letters and see whether the letters in the encrypted text resemble typically Dutch or English writing. Also, each letter in the encrypted text only has 26 possibilities in the decrypted text, including itself. You can also make a table in which you write down the text and let a computer replace each letter with all 26 possibilities.
Up until the 1970s, cryptographers made use of this type of cryptography – also known as symmetric cryptography.
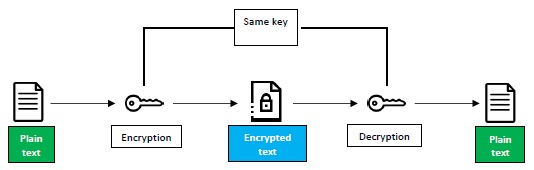
With symmetric cryptography, there is one key (the secret key) that is used for encrypting and decrypting the message. It’s therefore necessary for the sender of the message to share the secret key with the party he would like to correspond with.
The Caesar cipher is considered to be symmetric cryptography, because knowing the exact rotation (secret key) that is used to encrypt the message, you do also know how to decrypt the message.
Disadvantages of symmetric cryptography
There are several disadvantages to symmetric cryptography.
The first disadvantage is that the secret key has to be shared between the sender and receiver for messages to be exchanged privately. Sending the secret key over an unprotected communication channel is not recommended. In the next post, we will see how asymmetric (public key) cryptography allows us to send the encryption key safely over unprotected communication channels, while keeping the decryption key safely in our own possession.
The second disadvantage is that the secret key is now on two different locations. Thus, there are now two points of attack.
The third disadvantage is that the sender has to trust the receiver that he will not steal or copy the key or give it to someone else. It’s comparable to sharing the keys to your apartment: you also have to trust the other person not to steal your key, or copy your key, or give the key to another person.
The fourth disadvantage is limited scalability. Assuming that we’d like to communicate with a great number of parties, and that we’d like to provide each party with a different secret key for security reasons, we’d need to maintain a database of secret keys. For this setup to be user friendly in an environment like the internet, it would probably require an infrastructure of specialized distribution centers that generate secret keys each time two parties would like to initiate a private conversation. As these distribution centers would hold many secret keys, it would be a honey pot for hackers.
An example of symmetric cryptography is the Data Encryption Standard (DES), which was released on the market in 1975. It was developed by IBM, and was primarily meant to protect electronic communication between large financial organizations. Up until DES, cryptography was mainly a field for governments’ secret intelligence agencies to protect state communication. When the DES was released, it was received very well by cryptographers, until people found out that the National Security Agency (NSA) was involved with the development of the encryption key and purposefully influenced IBM to limit the key sizes from 64 bits to 56 bits. With 56 bits, there are 2^56 possible key combinations. This is considerably less than 64 bits keys. It is therefore much easier to break the encryption. Cryptographers believed that it would just be a matter of time before someone would find the right keys through a brute force search – meaning that you are trying all possible key combinations to find the right one.
Symmetric cryptography was the way cryptography was done until 1976 when two young researchers from Stanford University, Whitfield Diffie and Martin Hellman, invented asymmetric or public key cryptography.
Both researchers were discontent with DES, and Hellman even addressed a letter to the Secretary of Commerce, Elliot Richardson, saying:
I am writing to you because I am very worried that the National Security Agency has surreptitiously influenced the National Bureau of Standards [NBS] in a way which seriously limit the value of a proposed standard, and which may pose a threat to individual privacy. I refer to the proposed Data Encryption Standard. … I am convinced that NSA in its role of helping NBS design and evaluate possible standards has ensured that the proposed standard is breakable by NSA.
In my next post, I will discuss how public key cryptography works. Eventually, at the end of the post series, you will be able to encrypt your e-mails using public key cryptography.
When the government obtains its intended back door into all of our messages, how long will it be before we know?
[…] https://notesonliberty.com/2020/01/13/protecting-your-privacy-symmetric-cryptography-part-1/ […]
“Also, each letter in the encrypted text only has 25 possibilities in the decrypted text.”
No, each letter has 26 possibilities, including itself. Forbidding a letter ever to map to itself makes breaking encryption easier. Apparently the German Enigma machine made this mistake, and Alan Turing exploited that weakness to decipher the code (according to a movie on Turing’s life).
Ah, thanks for pointing that out! I’ve corrected it.
[…] my previous post, I mentioned four disadvantages of symmetric cryptography. These disadvantages […]